|
| 1 | +--- |
| 2 | +title: "Dev Tools for API Testing: What to Standardize Across Teams" |
| 3 | +date: "2026-02-22" |
| 4 | +slug: "dev-tools-for-api-testing-what-to-standardize-across-teams" |
| 5 | +id: "22d7ac5c-271a-4735-b7fe-f617a38476d6" |
| 6 | +image: |
| 7 | + url: "https://kccqmbkylzrrhibpxtbk.supabase.co/storage/v1/object/public/public-user-assets/b460f601-795d-47ba-abf4-41fb76ccea6f/22d7ac5c-271a-4735-b7fe-f617a38476d6/main-image.webp" |
| 8 | + alt: "Dev Tools for API Testing: What to Standardize Across Teams" |
| 9 | +author: |
| 10 | + name: "DevTools Team" |
| 11 | + avatar: "/logo.svg" |
| 12 | +tags: ["ci","yaml","workflow","api-testing","github-actions","variables"] |
| 13 | +category: "CI/CD" |
| 14 | +summary: "Dev Tools for API Testing: standardize YAML flows, Git conventions, CI reports, request chaining, and assertions so teams ship deterministic tests at scale." |
| 15 | +cta: |
| 16 | + primary: |
| 17 | + heading: "Standardize YAML API tests in CI" |
| 18 | + body: "Use a shared CI contract for YAML flows: deterministic runs, consistent exit codes, and predictable reports across repos and teams." |
| 19 | + buttonText: "Set up CI integrations" |
| 20 | + url: "https://dev.tools/docs/how-to/ci-integrations/" |
| 21 | + secondaryText: "GitHub Actions template" |
| 22 | + secondaryUrl: "https://dev.tools/templates/github-actions/" |
| 23 | + secondary: |
| 24 | + heading: "Make env + variables consistent" |
| 25 | + body: "Define a stable env var contract, overrides, and secret handling so flows run the same locally and in CI." |
| 26 | + buttonText: "Env & variables guide" |
| 27 | + url: "https://dev.tools/docs/how-to/environments-and-variables/" |
| 28 | + secondaryText: "Working with flows" |
| 29 | + secondaryUrl: "https://dev.tools/docs/how-to/working-with-flows/" |
| 30 | + badge: |
| 31 | + text: "Team standards" |
| 32 | + variant: "neutral" |
| 33 | +--- |
| 34 | + |
| 35 | +API testing falls apart at scale for predictable reasons: every team invents its own folder layout, environment variable names, chaining conventions, assertion style, and CI reporting. The result is not “more tests”, it is **more entropy**. You get brittle flows, noisy diffs, and PRs nobody can confidently review. |
| 36 | + |
| 37 | +Standardization is the fix, but not in the “everyone writes identical tests” sense. What you want is **a shared contract for how tests are expressed, reviewed, and executed** so any engineer can open a PR, understand the intent, and trust the CI signal. |
| 38 | + |
| 39 | +DevTools fits well here because it keeps API tests as **native YAML** (not a UI-locked format or a custom DSL), which makes standards enforceable via Git workflows, CODEOWNERS, linters, and normal code review. This article focuses on what to standardize across teams when your API tests are YAML-first and CI-native. |
| 40 | + |
| 41 | +## What “standardize” should mean (and what it should not) |
| 42 | + |
| 43 | +Standardization should define: |
| 44 | + |
| 45 | +- **Interfaces**: file layout, naming, env variables, how chaining works, how assertions are written. |
| 46 | +- **Determinism rules**: what is forbidden (volatile headers, wall-clock assertions as merge gates, shared state). |
| 47 | +- **CI contract**: exit codes, report formats, artifact paths, and what gets uploaded. |
| 48 | + |
| 49 | +Standardization should not define: |
| 50 | + |
| 51 | +- Exact endpoints or payloads. |
| 52 | +- The one true test suite structure for every service. |
| 53 | +- “Framework magic” that hides request dependencies. |
| 54 | + |
| 55 | +If you are migrating from Postman/Newman or Bruno, this is the core difference: instead of standardizing how people click around a GUI (or a tool-specific export format), you standardize a **Git-reviewed YAML representation** that CI runs exactly the same way every time. |
| 56 | + |
| 57 | +## Standardize the repo layout (so suites compose cleanly) |
| 58 | + |
| 59 | +Pick a layout that works for monorepos and polyrepos, supports sharding, and makes it obvious what is safe to commit. |
| 60 | + |
| 61 | +A pragmatic baseline: |
| 62 | + |
| 63 | +```text |
| 64 | +api-tests/ |
| 65 | + flows/ |
| 66 | + smoke/ |
| 67 | + regression/ |
| 68 | + env/ |
| 69 | + local.env |
| 70 | + ci.env |
| 71 | + staging.env |
| 72 | + prod.env |
| 73 | + env.example |
| 74 | + fixtures/ |
| 75 | + requests/ |
| 76 | + responses/ |
| 77 | + scripts/ |
| 78 | + redact-har.sh |
| 79 | + seed-test-data.sh |
| 80 | + .gitignore |
| 81 | +``` |
| 82 | + |
| 83 | +Key decisions to standardize: |
| 84 | + |
| 85 | +- **Flow file granularity**: prefer many small flows over a few giant suites. This makes CI sharding deterministic and reduces merge conflicts. |
| 86 | +- **Smoke vs regression definition**: “smoke” should be fast and safe to run on every PR. “regression” is broader and may run on merge, nightly, or by label. |
| 87 | +- **HAR hygiene**: if you generate flows from browser traffic, standardize that raw `.har` files are not committed (commit the sanitized YAML). DevTools already leans into this workflow via HAR to YAML conversion. |
| 88 | + |
| 89 | +If you want the CI implications and parallelization mechanics, DevTools has a deeper guide on pipeline-native execution in [API Testing in CI/CD](https://dev.tools/guides/api-testing-ci-cd/). |
| 90 | + |
| 91 | +## Standardize the environment variable contract (names, scoping, and overrides) |
| 92 | + |
| 93 | +Most “tool migrations” fail because each team invents different variable names and secret handling. Standardize the environment contract once, and treat it like an API. |
| 94 | + |
| 95 | +### Required variables: define a stable minimum |
| 96 | + |
| 97 | +A common baseline that scales: |
| 98 | + |
| 99 | +- `BASE_URL` |
| 100 | +- `AUTH_TOKEN` (optional, if your flows obtain tokens via login chaining, do not require this) |
| 101 | +- `CLIENT_ID`, `CLIENT_SECRET` (if using OAuth client credentials) |
| 102 | +- `TENANT_ID` (if multi-tenant) |
| 103 | +- `CI_RUN_ID` (for uniqueness) |
| 104 | + |
| 105 | +Create an `env.example` that documents required keys and expected formats, and make CI fail fast if they are missing. |
| 106 | + |
| 107 | +### Secrets policy: never commit, never bake into YAML |
| 108 | + |
| 109 | +Standardize: |
| 110 | + |
| 111 | +- Secrets come from CI secret stores (GitHub Actions Secrets, Vault, cloud secret managers). |
| 112 | +- YAML references secrets only via env var interpolation. |
| 113 | +- Recorded traffic must be sanitized (cookies, authorization headers, PII). If you are doing HAR capture, align on a redaction checklist. DevTools has a dedicated guide for this: [How to Redact HAR Files Safely](https://dev.tools/blog/how-to-redact-har-files-safely-keep-tests-shareable-remove-secrets/). |
| 114 | + |
| 115 | +### Base URL policy: no hardcoded hostnames |
| 116 | + |
| 117 | +Hardcoded URLs are the fastest way to end up with “works on my staging” tests. |
| 118 | + |
| 119 | +A minimal pattern: |
| 120 | + |
| 121 | +```yaml |
| 122 | +# flows/smoke/health.yaml |
| 123 | +steps: |
| 124 | + - id: health |
| 125 | + request: |
| 126 | + method: GET |
| 127 | + url: ${BASE_URL}/health |
| 128 | + assert: |
| 129 | + status: 200 |
| 130 | +``` |
| 131 | +
|
| 132 | +Even if your runner supports defaults, standardize explicitness. It keeps flows portable across repos and execution contexts. |
| 133 | +
|
| 134 | +## Standardize step naming (because reporting depends on it) |
| 135 | +
|
| 136 | +Your CI report is only as useful as the names it emits. |
| 137 | +
|
| 138 | +Standardize a naming scheme that is: |
| 139 | +
|
| 140 | +- Stable over time |
| 141 | +- Unique across the repo |
| 142 | +- Mappable to ownership boundaries |
| 143 | +
|
| 144 | +A simple convention: |
| 145 | +
|
| 146 | +- **Flow path indicates suite** (smoke vs regression) |
| 147 | +- **Step `id` indicates intent** (not just endpoint) |
| 148 | + |
| 149 | +Example: |
| 150 | + |
| 151 | +```yaml |
| 152 | +# flows/regression/billing/invoice-lifecycle.yaml |
| 153 | +steps: |
| 154 | + - id: auth.login |
| 155 | + - id: invoice.create |
| 156 | + - id: invoice.get |
| 157 | + - id: invoice.void |
| 158 | + - id: invoice.verify_voided |
| 159 | +``` |
| 160 | + |
| 161 | +This pays off when emitting JUnit (or similar) because your failures show up as meaningful test cases instead of “Request 7 failed”. If you want a detailed, CI-focused treatment, see [JUnit Reports for API Tests](https://dev.tools/blog/junit-reports-for-api-tests-make-github-actions-show-failures-cleanly/). |
| 162 | + |
| 163 | +## Standardize request chaining (make dependencies explicit) |
| 164 | + |
| 165 | +Chaining is where teams most often drift into hidden state and flakiness. Standardize the “data flow rules” so reviewers can reason about the sequence. |
| 166 | + |
| 167 | +### Rule: extract once, reference everywhere |
| 168 | + |
| 169 | +Prefer a single extraction point for IDs/tokens, and reference that variable downstream. |
| 170 | + |
| 171 | +Representative pattern: |
| 172 | + |
| 173 | +```yaml |
| 174 | +steps: |
| 175 | + - id: auth.login |
| 176 | + request: |
| 177 | + method: POST |
| 178 | + url: ${BASE_URL}/api/login |
| 179 | + headers: |
| 180 | + content-type: application/json |
| 181 | + body: |
| 182 | + username: ${USERNAME} |
| 183 | + password: ${PASSWORD} |
| 184 | + extract: |
| 185 | + access_token: $.accessToken |
| 186 | + assert: |
| 187 | + status: 200 |
| 188 | +
|
| 189 | + - id: invoice.create |
| 190 | + depends_on: [auth.login] |
| 191 | + request: |
| 192 | + method: POST |
| 193 | + url: ${BASE_URL}/api/invoices |
| 194 | + headers: |
| 195 | + authorization: Bearer ${access_token} |
| 196 | + content-type: application/json |
| 197 | + body: |
| 198 | + externalRef: ${CI_RUN_ID} |
| 199 | + amountCents: 499 |
| 200 | + extract: |
| 201 | + invoice_id: $.id |
| 202 | + assert: |
| 203 | + status: 201 |
| 204 | +
|
| 205 | + - id: invoice.get |
| 206 | + depends_on: [invoice.create] |
| 207 | + request: |
| 208 | + method: GET |
| 209 | + url: ${BASE_URL}/api/invoices/${invoice_id} |
| 210 | + headers: |
| 211 | + authorization: Bearer ${access_token} |
| 212 | + assert: |
| 213 | + status: 200 |
| 214 | + json: |
| 215 | + - path: $.id |
| 216 | + equals: ${invoice_id} |
| 217 | +``` |
| 218 | + |
| 219 | +Standardization points: |
| 220 | + |
| 221 | +- **Dependency declaration** (`depends_on` or equivalent) is required when one step consumes another step’s outputs. |
| 222 | +- **No reliance on cookie jars or implicit session state** unless the flow explicitly asserts it. |
| 223 | +- **Correlation for uniqueness**: mandate a per-run identifier (`CI_RUN_ID`) used in create operations to avoid collisions in parallel CI. |
| 224 | + |
| 225 | +DevTools already leans into chaining patterns and multi-step flows. If you want deeper workflow patterns (polling, branching, loops), see [API Workflow Automation: Testing Multi-Step Business Logic](https://dev.tools/guides/api-workflow-automation/). |
| 226 | + |
| 227 | +## Standardize assertion strategy (invariants first, snapshots selectively) |
| 228 | + |
| 229 | +Teams tend to either under-assert (“status 200”) or over-assert (full payload snapshots that flake). Standardize what “good” looks like. |
| 230 | + |
| 231 | +A workable policy for most API suites: |
| 232 | + |
| 233 | +| Assertion type | Standardize when to use | What to avoid | |
| 234 | +|---|---|---| |
| 235 | +| Status + key headers | Every request | Ignoring caching / content-type regressions | |
| 236 | +| JSON invariants (JSONPath) | Default for response bodies | Exact matching of volatile fields (timestamps, IDs you did not create) | |
| 237 | +| Schema/contract checks | Broad coverage, especially for public APIs | Treating schema as a substitute for workflow correctness | |
| 238 | +| Snapshots (golden responses) | Only for complex nested payloads that are hard to assert | Raw snapshots without canonicalization/redaction | |
| 239 | + |
| 240 | +For error responses, standardize a contract. If you use RFC 7807 problem details, assert the structure and stable fields (type, title, status), see [RFC 7807](https://www.rfc-editor.org/rfc/rfc7807). |
| 241 | + |
| 242 | +If your teams are debating schema vs snapshots, DevTools has a CI-grounded discussion here: [Schema vs Snapshot Testing for APIs](https://dev.tools/blog/schema-vs-snapshot-testing-for-apis-what-actually-works-in-ci/). |
| 243 | + |
| 244 | +## Standardize determinism guardrails (what reviewers must block) |
| 245 | + |
| 246 | +This is the part that separates a test suite from a CI liability. |
| 247 | + |
| 248 | +### Volatile request data |
| 249 | + |
| 250 | +Standardize a denylist for headers and fields that should not appear unless justified: |
| 251 | + |
| 252 | +- `User-Agent`, `sec-*`, `accept-language` (browser noise) |
| 253 | +- Dynamic tracing headers that change every request (unless you intentionally assert propagation) |
| 254 | +- Cookies captured from a browser session (replace with explicit auth chaining) |
| 255 | + |
| 256 | +### Time and polling |
| 257 | + |
| 258 | +Standardize: |
| 259 | + |
| 260 | +- Polling loops must have **bounded attempts** and a clear timeout. |
| 261 | +- Timing assertions are budgets, not hard gates, unless you have stable performance environments. |
| 262 | + |
| 263 | +### Retries |
| 264 | + |
| 265 | +Retries should be scoped. Standardize that retries are allowed for: |
| 266 | + |
| 267 | +- Network timeouts |
| 268 | +- 429 rate limits (with backoff) |
| 269 | + |
| 270 | +Retries should not mask deterministic failures (400, 401, 403, assertion failures). |
| 271 | + |
| 272 | +If you want a CI-specific playbook for secrets/auth/retries/rate limits, see [API Testing in GitHub Actions: Secrets, Auth, Retries, Rate Limits](https://dev.tools/blog/api-testing-in-github-actions-secrets-auth-retries-rate-limits/). |
| 273 | + |
| 274 | +## Standardize parallel safety (data isolation and cleanup) |
| 275 | + |
| 276 | +Once you run tests in parallel (or multithreaded locally), shared mutable state becomes your biggest flake source. |
| 277 | + |
| 278 | +Standardize the following rules: |
| 279 | + |
| 280 | +- **Each flow owns its data**: create unique resources, assert, then cleanup. |
| 281 | +- **Unique naming**: prefix created entities with `${CI_RUN_ID}` (or a generated suffix) so parallel jobs do not collide. |
| 282 | +- **Idempotency where possible**: use idempotency keys for create endpoints that support them. |
| 283 | +- **Teardown is non-optional** for suites that run on shared environments. |
| 284 | + |
| 285 | +A practical cleanup pattern: |
| 286 | + |
| 287 | +```yaml |
| 288 | +steps: |
| 289 | + - id: widget.create |
| 290 | + # ...extract widget_id... |
| 291 | +
|
| 292 | + - id: widget.delete |
| 293 | + depends_on: [widget.create] |
| 294 | + request: |
| 295 | + method: DELETE |
| 296 | + url: ${BASE_URL}/api/widgets/${widget_id} |
| 297 | + headers: |
| 298 | + authorization: Bearer ${access_token} |
| 299 | + assert: |
| 300 | + status: 204 |
| 301 | +``` |
| 302 | + |
| 303 | +For more on making multi-request sequences deterministic, see [API Chain Testing](https://dev.tools/blog/api-chain-testing-how-to-test-multi-request-sequences-automatically/). |
| 304 | + |
| 305 | +## Standardize CI output (reports, artifacts, exit codes) |
| 306 | + |
| 307 | +If different repos emit different artifacts, platform teams cannot build reliable dashboards, and engineers cannot debug failures quickly. |
| 308 | + |
| 309 | +Define a single contract for every CI run: |
| 310 | + |
| 311 | +- Always emit JUnit XML to a known path. |
| 312 | +- Always emit machine-readable JSON (optional, but helpful for custom tooling). |
| 313 | +- Always upload runner logs as artifacts on failure. |
| 314 | +- Always exit non-zero on assertion failures. |
| 315 | + |
| 316 | +A simple “commit vs artifact” standard helps prevent repo bloat and security leaks: |
| 317 | + |
| 318 | +| Item | Store where | Why | |
| 319 | +|---|---|---| |
| 320 | +| YAML flows | Git | Reviewable, diffable source of truth | |
| 321 | +| env templates (`env.example`) | Git | Onboarding and determinism | |
| 322 | +| Raw HAR | Not in Git | High risk for secrets/PII, noisy | |
| 323 | +| JUnit XML | CI artifact | Debuggable failures, PR annotations | |
| 324 | +| Full logs | CI artifact | Post-mortems without reruns | |
| 325 | + |
| 326 | +If you are standardizing on GitHub Actions, also standardize version pinning (runner images, actions, CLIs) to avoid silent breakage. See [Pinning GitHub Actions + Tool Versions](https://dev.tools/blog/pinning-github-actions-tool-versions-stop-ci-breakage-devtools-included/). |
| 327 | + |
| 328 | +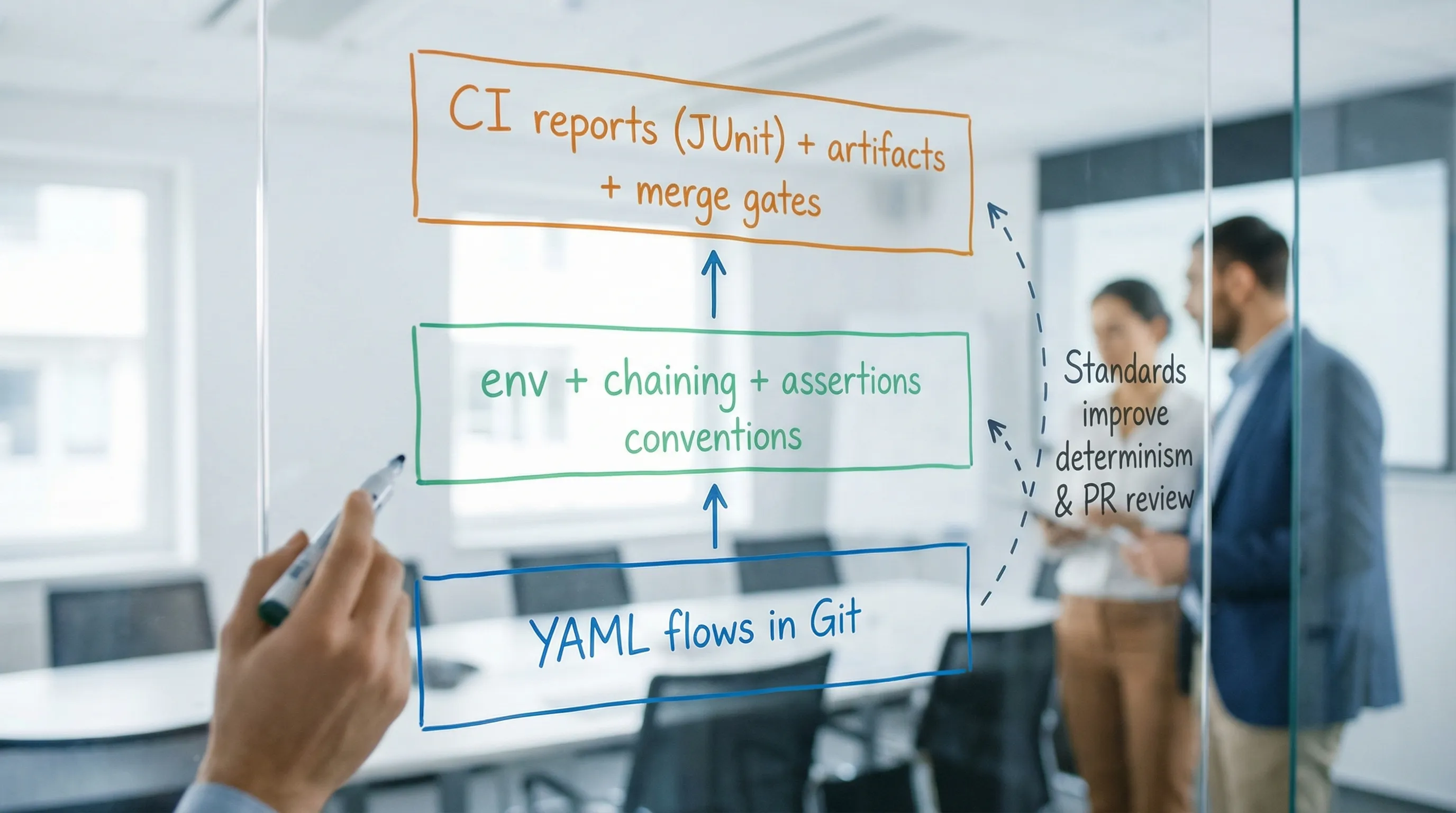 |
| 329 | + |
| 330 | +## Standardize governance (ownership, review gates, and enforcement) |
| 331 | + |
| 332 | +Standards that live in a wiki die. Standards that are enforced in Git survive. |
| 333 | + |
| 334 | +Practical governance that experienced teams use: |
| 335 | + |
| 336 | +- **CODEOWNERS for suites**: route changes in `flows/regression/billing/` to the billing team. |
| 337 | +- **PR template checklist**: “no secrets, no hardcoded base URLs, explicit dependencies, deterministic assertions, cleanup.” |
| 338 | +- **Pre-commit hooks**: reject committed `.har`, run YAML formatting checks, block accidental secret patterns. |
| 339 | +- **CI lint job**: fail on missing required env keys, unpinned versions, or disallowed headers. |
| 340 | + |
| 341 | +If you want a review-focused checklist that aligns with YAML-first testing, DevTools has a dedicated guide: [Codes Review Checklist for YAML API Tests (No UI Required)](https://dev.tools/blog/codes-review-checklist-for-yaml-api-tests-no-ui-required/). |
| 342 | + |
| 343 | +## Tooling reality check: Postman/Newman, Bruno, and native YAML |
| 344 | + |
| 345 | +Standardization is easier when your test format is stable, reviewable, and not mediated by a UI. |
| 346 | + |
| 347 | +### Postman + Newman |
| 348 | + |
| 349 | +- Collections are fundamentally a **tool-owned format**. You can export JSON, but it is not optimized for human diffs. |
| 350 | +- Teams often end up with “CI scripts” that depend on Postman-specific behaviors, plus brittle pre-request scripting. |
| 351 | +- Review is hard: diffs are noisy, ordering changes happen, and intent is buried. |
| 352 | + |
| 353 | +### Bruno |
| 354 | + |
| 355 | +- Bruno is file-based and Git-friendlier than many GUI tools. |
| 356 | +- But it still introduces a tool-specific representation and conventions you must standardize around. |
| 357 | + |
| 358 | +### DevTools (YAML-first) |
| 359 | + |
| 360 | +- Native YAML keeps tests **readable and portable** across teams. |
| 361 | +- Chaining and determinism conventions can be encoded as code review norms and CI checks. |
| 362 | +- HAR to YAML workflows give you a realistic starting point, then your standards shape the output into maintainable flows. |
| 363 | + |
| 364 | +If your organization is actively replacing Newman, the DevTools-specific migration path is covered in [Newman alternative for CI: DevTools CLI](https://dev.tools/guides/newman-alternative-ci/). |
| 365 | + |
| 366 | +## A practical “team standard” you can actually adopt |
| 367 | + |
| 368 | +If you want this to stick, write a short standard (1 to 2 pages) and enforce it in CI. Keep it concrete: |
| 369 | + |
| 370 | +- **Repo layout**: where flows, env, fixtures live |
| 371 | +- **Env contract**: required variables and naming |
| 372 | +- **Chaining rules**: explicit dependencies, extract once |
| 373 | +- **Assertions policy**: invariants first, snapshots selectively |
| 374 | +- **Determinism guardrails**: banned headers, bounded polling, scoped retries |
| 375 | +- **Parallel safety**: unique IDs, cleanup required |
| 376 | +- **CI contract**: JUnit path, artifact retention, exit codes |
| 377 | +- **Governance**: CODEOWNERS, PR checklist, lint rules |
| 378 | + |
| 379 | +That is the difference between “we have API tests” and “we have an API test system” that multiple teams can evolve without breaking each other. |
0 commit comments