microlink.io handles +700M requests every month.
When you're building infrastructure that needs an URL as input for getting data, you’re constantly interacting with defenses designed to stop you.
A request can experience429 TOO_MANY_REQUESTS401 UNAUTHORIZED403 FORBIDDEN
Followed by a challenge page. A captcha. A JavaScript puzzle.
Modern antibot systems operate at multiple layers, often before your request even reaches the application code.
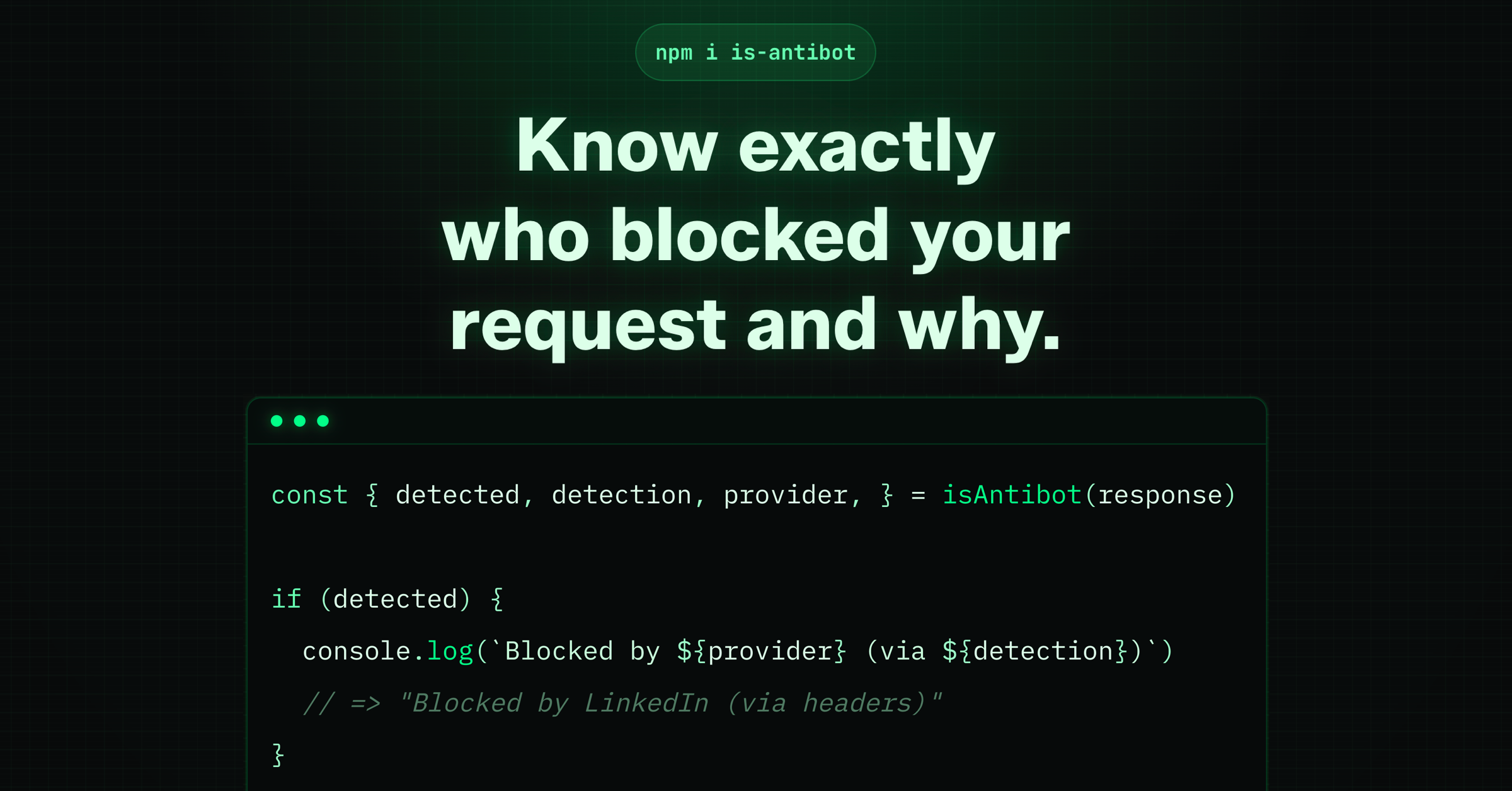
Our library is-antibot does something fundamental: it tells you when a non-success resolution happens and who triggered it, so you can make a better decision about what to do next.
blocked providers recaptcha akamai cloudflare-turnstile aws-waf akamai hcaptchaCommon signals include:
- IP reputation: Data-center IPs are flagged by default. Residential traffic behaves differently.
- HTTP consistency: Headers must match a real browser profile—not just User-Agent, but the full set.
- TLS fingerprints (JA3): The way a client negotiates TLS leaks whether it’s a browser or a script.
- Behavioral heuristics: Timing, navigation order, and interaction patterns matter.
- JavaScript fingerprinting: Canvas, WebGL, fonts, screen size—small inconsistencies are enough.
Based on these signals, a request is either:
- Allowed: If the heuristics indicate a legitimate human visitor, the request is passed through to the target website.
- Blocked: If the request is highly suspicious (e.g., coming from a known malicious IP or with a broken TLS fingerprint), it is blocked immediately with a 403 Forbidden or 429 Too Many Requests error.
- Challenged: If the system is unsure, it serves a “challenge”—such as a CAPTCHA or a JavaScript-based interstitial—that must be resolved before the actual content is released.
Install it as dependency is the first thing to do:
npm install is-antibotis-antibot is designed to have a minimal footprint. It works with static HTTP response analysis.
No headless browser is required. Just pass it the response information:
import isAntibot from 'is-antibot'
const response = await fetch('https://example.com')
const { detected, provider, detection } = isAntibot({
headers: response.headers,
statusCode: response.status,
html: await response.text(),
url: response.url
})
if (detected) {
console.log(`Blocked by ${provider} (via ${detection})`)
// => "Blocked by CloudFlare (via headers)"
}The result is deterministic and fast—designed to run on every request without becoming the bottleneck.
It works with any HTTP client, including got, axios, undici or just the vanilla fetch.
At a high level, is-antibot classifies challenge responses using:
- HTTP status patterns: Certain platforms use unusual status codes when blocking automation; for example, LinkedIn can return
999and Reddit can return403on challenge flows. - Known challenge signatures: Challenge pages often include recognizable artifacts like CAPTCHA widgets, interstitial templates, or verification scripts.
- Response headers and body markers: Blocking responses usually expose hints in headers and HTML, such as mitigation headers, challenge tokens, or provider-specific script references.
- Provider-specific fingerprints: Each provider leaves a distinct combination of signals; for example, Cloudflare commonly surfaces
cf-mitigated: challenge, while other providers rely more on cookie, URL, or HTML fingerprints.
Each provider has unique fingerprints across one or more of these signals. The library checks them in priority order and returns the first match.
is-antibot currently detects challenges across antibot systems, CAPTCHA vendors, and platform-specific protection flows.
| Provider | Category | Signals | Detection methods |
|---|---|---|---|
| Akamai | Antibot | 3 | HeadersCookiesHTML |
| AliExpress CAPTCHA | CAPTCHA | 2 | HTMLURL |
| Anubis | Antibot | 1 | HTML |
| AWS WAF | Antibot | 3 | HeadersCookiesHTML |
| Captcha.eu | CAPTCHA | 2 | HTMLURL |
| Cheq | Antibot | 2 | HTMLURL |
| Cloudflare | Antibot | 2 | HeadersCookies |
| Cloudflare Turnstile | CAPTCHA | 2 | HTMLURL |
| DataDome | Antibot | 2 | HeadersCookies |
| Friendly Captcha | CAPTCHA | 2 | HTMLURL |
| FunCaptcha (Arkose Labs) | CAPTCHA | 2 | HTMLURL |
| GeeTest | CAPTCHA | 2 | HTMLURL |
| hCaptcha | CAPTCHA | 2 | HTMLURL |
| Imperva / Incapsula | Antibot | 3 | HeadersCookiesHTML |
| Platform-specific | 1 | HTML | |
| Kasada | Antibot | 2 | HeadersHTML |
| Platform-specific | 1 | Status Code | |
| Meetrics | Antibot | 2 | HTMLURL |
| Ocule | Antibot | 2 | HTMLURL |
| PerimeterX | Antibot | 3 | HeadersCookiesHTML |
| QCloud Captcha | CAPTCHA | 2 | HTMLURL |
| reCAPTCHA | CAPTCHA | 2 | HTMLURL |
| Reblaze | Antibot | 2 | CookiesHTML |
| Platform-specific | 2 | HTMLStatus Code | |
| Shape Security | Antibot | 2 | HeadersHTML |
| Sucuri | Antibot | 1 | HTML |
| ThreatMetrix | Antibot | 2 | HTMLURL |
| Vercel | Antibot | 1 | Headers |
| YouTube | Platform-specific | 1 | HTML |
Use this table as a quick coverage map when building retry logic, escalation rules, or provider-specific analytics in your scraping pipeline.
In case you are missing a provider or signal detection, please report to us, and we will continue evolving the library.