Releases: yashab-cyber/hackbot
HackBot v1.2.3 — Zero-Day Discovery Engine
HackBot v1.2.3
🔬 Zero-Day Discovery Engine (NEW)
A brand-new intelligence module that turns HackBot from a "known-CVE scanner" into a proactive vulnerability researcher:
- Response Anomaly Detection — 40+ regex patterns across 7 categories automatically scan every tool output for stack traces, error leaks, path disclosures, debug info, memory addresses, auth leaks, and injection signals
- Smart Fuzz Payload Generator — 150+ payloads across 12 categories: buffer overflow, integer overflow, path traversal, SSTI, SSRF, deserialization, command injection, XSS, header injection, XXE, request smuggling, race conditions
- Exploit Chain Builder — Analyzes multiple findings to propose high-impact attack chains (SSRF→RCE, SQLi→WebShell, LFI→Log Poisoning→RCE, XSS→CSRF→Account Takeover, and more)
- Version Gap Analysis — Flags services where the exact version has no known CVE but nearby versions do — zero-day candidates
- Auto-Enrichment — Every tool execution output is automatically analyzed for zero-day signals with no extra configuration needed
- New Agent Actions — AI can now invoke
fuzz,analyze_anomaly, andchain_exploitsactions autonomously during assessments
🛠️ Expanded Tool Support (+20 tools)
New tools added to the default allowed list (56 → 76 total):
- Web Security:
wpscan,dalfox,commix,tplmap,ghauri,crlfuzz,jwt_tool,xxeinjector - Recon/Discovery:
arjun,paramspider,katana,gau,waybackurls - Exploitation:
ysoserial - Scripting/Compilation:
python3,ruby,perl,php,gcc,go
🐛 Bug Fixes
- Fixed: "Cannot read property 'appendChild' of null" error when stopping the agent — all 7 references to non-existent
agentMessageselement replaced with the existingagentThoughtscontainer - Fixed:
startCampaignTargetnull pointer crash when starting campaign targets - Fixed: Incorrect CSS class names in campaign target message rendering (now uses
msg msg-assistant) - Added: Null guards for all DOM manipulation in agent panel functions
📖 Documentation
- New manual chapter:
15-zeroday-engine.md— comprehensive guide with architecture, all payload categories, exploit chains, and API reference - Updated:
README.md— features table, agent mode description, GUI features, new intelligence module section - Updated:
05-intelligence-modules.md— Zero-Day Engine as first module (9 → 10 modules) - Updated:
04-modes.md— Agent methodology now includes zero-day analysis phases - Updated:
03-gui-reference.md— Agent panel docs with zero-day features - Updated:
09-configuration.md— Expanded tools list (56 → 76)
Files Changed
| File | Change |
|---|---|
hackbot/core/zeroday.py |
NEW — Zero-Day Discovery Engine module |
hackbot/core/engine.py |
Enhanced agent system prompt with zero-day hunting protocol |
hackbot/modes/agent.py |
Integrated ZeroDayEngine — 3 new action handlers, auto-enrichment |
hackbot/config.py |
20 new tools in default allowed list |
hackbot/core/__init__.py |
Export ZeroDayEngine |
hackbot/gui/templates/index.html |
Fixed agent DOM errors + updated descriptions |
manual/15-zeroday-engine.md |
NEW — Dedicated manual chapter |
manual/README.md |
Added chapter 15 to table of contents |
manual/03-gui-reference.md |
Zero-day features in agent panel |
manual/04-modes.md |
Zero-day phases in agent methodology |
manual/05-intelligence-modules.md |
Full zero-day engine documentation |
manual/09-configuration.md |
Updated tools count and list |
README.md |
Feature table, agent mode, GUI features, intelligence section |
website/index.html |
Version bump |
Full Changelog: v1.2.2...v1.2.3
HackBot v1.2.2
HackBot v1.2.2
Highlights
- 🛡️ Stable Agent Execution — Resolved critical command validation issues.
- Fixed "BLOCKED: Tool is not in the allowed list" errors caused by double-sudo prefixing.
- Implemented automatic command repair for malformed AI-generated commands.
- Enhanced tool extraction logic to handle nested sudo and flag-like tokens accurately.
- 🖥️ UI Reliability Fixes — Restored Agent execution visibility.
- Fixed a bug where "EXECUTION STEPS" and "LIVE TERMINAL" panels remained empty during assessments.
- Corrected SSE streaming event handling in the GUI.
- 🧠 Improved AI Guidance — Enhanced system prompts for better autonomy.
- Updated Agent system instructions with concrete command examples and formatting rules.
- Explicitly prohibited sudo inclusions in AI-generated command fields for consistent handling.
Improvements & Bug Fixes
- Fixed normalization ordering in the tool runner (backticks vs. shell prompts).
- Added comprehensive test suite for agent command validation and sudo stripping (6+ new tests).
- Updated internal versioning across all core components.
Full Changelog
- Compare: v1.2.1...v1.2.2
HackBot v1.2.1
HackBot v1.2.1
Highlights
- 🚀 Agent Execution Logging & Replay System — Complete visibility into AI actions.
- Transparent tracking: Agent reasoning and thoughts are explicitly captured before JSON tool outputs.
- Persistent storage:
execution_log.jsonandexecution_log.txtautomatically exported to your sessions/reports folder.
- 🖥️ Live Output Panel Redesign — Real-time tracking of AI workflows:
- Beautiful 3-pane layout during active assessments.
- Left Pane: Chronological execution steps and tool statuses.
- Right Pane: Emulated terminal rendering
stdout/stderrsecurely. - Bottom Pane: Monitored AI reasoning and conversational thought-streams.
- ⏪ Interactive Replay Mode — Rewind and review past sessions:
- Dedicated player accessible from the "Sessions" tab.
- Full playback controls: Play, Pause, Next Step, Previous Step, and 1x-10x Speed Slider.
- Reconstructs accurate tool execution history dynamically.
- 📄 Enhanced PDF Reports — Fully auditable penetration testing trails:
- Appends
6. Agent Execution Logto all generated PDFs mapping chronological thoughts + logs for clients and debriefings.
- Appends
Tests
- Execution loop and real-time streaming mechanisms thoroughly verified.
- Playback consistency verified for complex, multi-round agent interactions.
Full Changelog
- Compare: v1.2.0...v1.2.1
v1.2.0
What we fixed
- Fixed an issue where the HackBot agent would enter an infinite loop trying to execute the same tool repeatedly without returning to the user.
- Implemented session-level and round-level deduplication for commands.
- Refined the nudge mechanism to correctly identify when the AI outputs actionable tool commands vs general chat.
HackBot v1.1.2
HackBot v1.1.2
Highlights
- Fixed tool validation for
sudo -n ...commands by correctly resolving the real executable after sudo flags. - Added loop-guard protection in Agent mode to stop repeated identical failing command retries.
- Improved Kali detection of
thc-ipv6by supporting alias binaries (for examplealive6). - Enhanced report outputs (HTML/Markdown/JSON/PDF) with:
- 4. List of Commands Executed (including whether sudo was used)
- 5. Technical Annex (Agent Output)
- Improved GUI startup diagnostics for missing native backends and fallback guidance.
- Added root/sudo GUI launch guard with clear remediation instructions.
Documentation
- Added Plugin Creation Guide and linked it in manual index.
- Updated plugin path documentation to
~/.config/hackbot/plugins/for consistency with runtime behavior. - Expanded GUI troubleshooting guidance for Qt/GTK backend dependencies and venv notes.
Tests
- Added regression coverage for sudo option parsing and alias tool resolution.
- Added report normalization checks for sudo markers and technical annex output.
Full Changelog
- Compare: v1.1.1...v1.1.2
HackBot v1.1.1
HackBot v1.1.1
New Features
- Added generated script support in Agent Mode with a new script action format.
- Added script persistence in assessment state and auto-save memory.
- Added a new Scripts panel in GUI to view generated scripts.
- Added GUI API endpoint for scripts: /api/agent/scripts.
- Added script inclusion in HTML, Markdown, JSON, and PDF reports.
- Added plugin marketplace button in GUI Plugins panel.
- Added official HackBot website link in GUI sidebar footer.
- Expanded default Kali/security tool allowlist (Metasploit, wireless, recon, sniffing, enum tools, and more).
- Added backward-compatible allowlist migration so existing configs auto-include newly added default tools.
- Added Telegram /tools command for installed, missing, and full tool inventory.
- Enhanced Telegram /config output with allowed tools summary and sample list.
Bug Fixes
- Fixed second-run tool execution reliability by normalizing fenced/prompt/backticked commands.
- Fixed tool allowlist checks to be case-insensitive and extension-normalized.
- Fixed tool name inference edge cases for malformed/empty commands.
- Fixed report export wiring to always use tool_history (Telegram regression).
- Fixed report output to include explicit Tool + Command in execution logs.
- Hardened agent action parsing so JSON actions are extracted reliably when script content contains braces.
- Fixed report generation paths to include generated scripts in CLI, GUI, and Telegram exports.
Tests and Docs
- Added/updated tests for runner normalization and case-insensitive tool allowlist behavior.
- Added/updated tests for report normalization and tool log rendering.
- Added/updated tests for config allowlist migration behavior.
- Added/updated tests for Telegram tools command registration and report generation keyword usage.
- Updated configuration manual with expanded default allowed tools list.
Full Changelog
- Compare: v1.1.0...v1.1.1
HackBot v1.1.0
HackBot v1.1.0
🚀 New Features
MITRE ATT&CK Mapping
- Map security findings and tool usage to the MITRE ATT&CK Enterprise framework
- 14 tactics, ~80 techniques, 30 finding regex rules, 26 tool mappings
- Export ATT&CK Navigator v4.5 layer JSON for visual analysis
- CLI:
/attackcommand with 7 subcommands (map, layer, summary, tactics, techniques, tool, lookup) - GUI: 7 new REST API endpoints under
/api/attack/* - Telegram:
/attackbot command with 5 subcommands - Automatic integration into agent PDF reports
- 70 new tests
Vulnerability Database
- Local SQLite database for persistent finding storage across assessments
- SHA-256 deduplication — same finding on same target tracked once
- 5 remediation statuses: open, in_progress, resolved, accepted, false_positive
- Full audit trail for every status change
- Risk scoring with severity weights (Critical 10.0 → Info 0.5)
- Risk trend tracking with point-in-time snapshots
- CLI:
/vulndbcommand with 12 subcommands (stats, search, target, severity, status, history, risk, assessments, export, purge, finding, targets) - GUI: 6 new REST API endpoints under
/api/vulndb/* - Telegram:
/vulndbbot command - 45 new tests
📊 Testing
- 724 tests passing across 16 test files (up from 384 in v1.0.1)
- New test files:
test_attack.py(70 tests),test_vulndb.py(45 tests)
📖 Documentation
- Comprehensive README updates with new feature sections, API endpoints, and architecture
- New manual pages:
11-attack-mapping.mdand12-vulnerability-database.md - Updated manual index and cross-references
🔗 Links
Full Changelog: v1.0.1...v1.1.0
HackBot v1.0.1 — Agent Mode Bugfix
Bug Fixes
Agent Mode: Follow-up Command Execution
Fixed a critical bug where the agent would not execute follow-up commands from AI analysis responses. For example, when nmap -sS failed due to missing root privileges and the AI suggested nmap -sT as a fallback, the command was never executed — the agent dropped back to the REPL prompt instead.
Root cause: The start() method never parsed the AI's analysis response for new action blocks, and the step() method only handled finding, generate_report, and complete actions in follow-up analysis — execute actions were silently ignored.
Changes
_process_actions_loop()— New method that chains command execution across multiple rounds (up to 10). When the AI responds to tool results with new execute actions, the loop continues automatically instead of returning to the REPL.- Strengthened system prompt — Made JSON action blocks mandatory with explicit instructions. Added
CRITICALsection and reminder to prevent AI from describing commands in plain text. _nudge_for_actions()— Fallback mechanism that re-prompts the AI when it describes commands in text without including required JSON action blocks.- Improved
_parse_actions()regex — Added 3 additional patterns to handle edge cases (missing trailing newlines, extra whitespace, flexible fence formatting).
Impact
The agent now runs fully autonomously through the complete assessment lifecycle: reconnaissance → scanning → enumeration → error recovery → findings → report generation — all without manual intervention.
HackBot v1.0.0 — Initial Release
🎉 HackBot v1.0.0 — Initial Production Release
⚡ Features
- 🤖 Agent Mode — Autonomous penetration testing with real tools, result analysis, and adaptive strategy
- 💬 Chat Mode — Interactive cybersecurity Q&A with streaming responses and conversation memory
- 📋 Plan Mode — 8 structured pentest plan templates, checklists, and attack methodologies
- 🖥️ Native Desktop GUI — Full-featured pywebview-powered dark theme graphical interface
- 🛡️ CVE/Exploit Lookup — Real-time NVD search + GitHub PoC discovery
- 🌐 OSINT Module — Subdomain enumeration, DNS recon, WHOIS, email harvesting, tech stack fingerprinting
- 🗺️ Network Topology — Interactive D3.js force-directed network visualization
- 📋 Compliance Mapping — Auto-map findings to PCI DSS v4.0, NIST 800-53, OWASP Top 10, ISO 27001
- 🔀 Diff Reports — Compare two assessments — see new, fixed, and persistent vulnerabilities
- 🎯 Multi-Target Campaigns — Define scope with multiple hosts/URLs for coordinated assessments
- 🧩 Custom Plugins — Python plugin system to register your own scripts as agent-callable tools
- 🔧 AI Remediation Engine — Auto-generate fix commands, config patches, and code snippets
- 🔌 HTTP Proxy / Traffic Capture — Built-in intercepting proxy for capturing, inspecting, and replaying web traffic
- 🧠 Memory & Sessions — Auto-save conversations, session history,
/continuetruncated responses - 🌍 10 AI Providers — OpenAI, Anthropic, Google Gemini, Groq, Mistral, DeepSeek, Together AI, OpenRouter, Ollama, Local
- 🔧 30+ Tool Integrations — nmap, nikto, sqlmap, nuclei, ffuf, subfinder, hydra, gobuster, and more
- 📊 Auto Reporting — HTML, Markdown, JSON, and professional PDF reports with executive summary and risk matrix
- 🛡️ Safe Mode — Command validation, blocked dangerous commands, risky-command confirmation prompts
- 💻 Cross-Platform — Linux, macOS, Windows — pip install, Docker, or one-line installer
- 🎨 Rich Terminal UI — Syntax highlighting, markdown rendering, progress indicators
📸 Screenshots
| CLI View | GUI View | Settings |
|---|---|---|
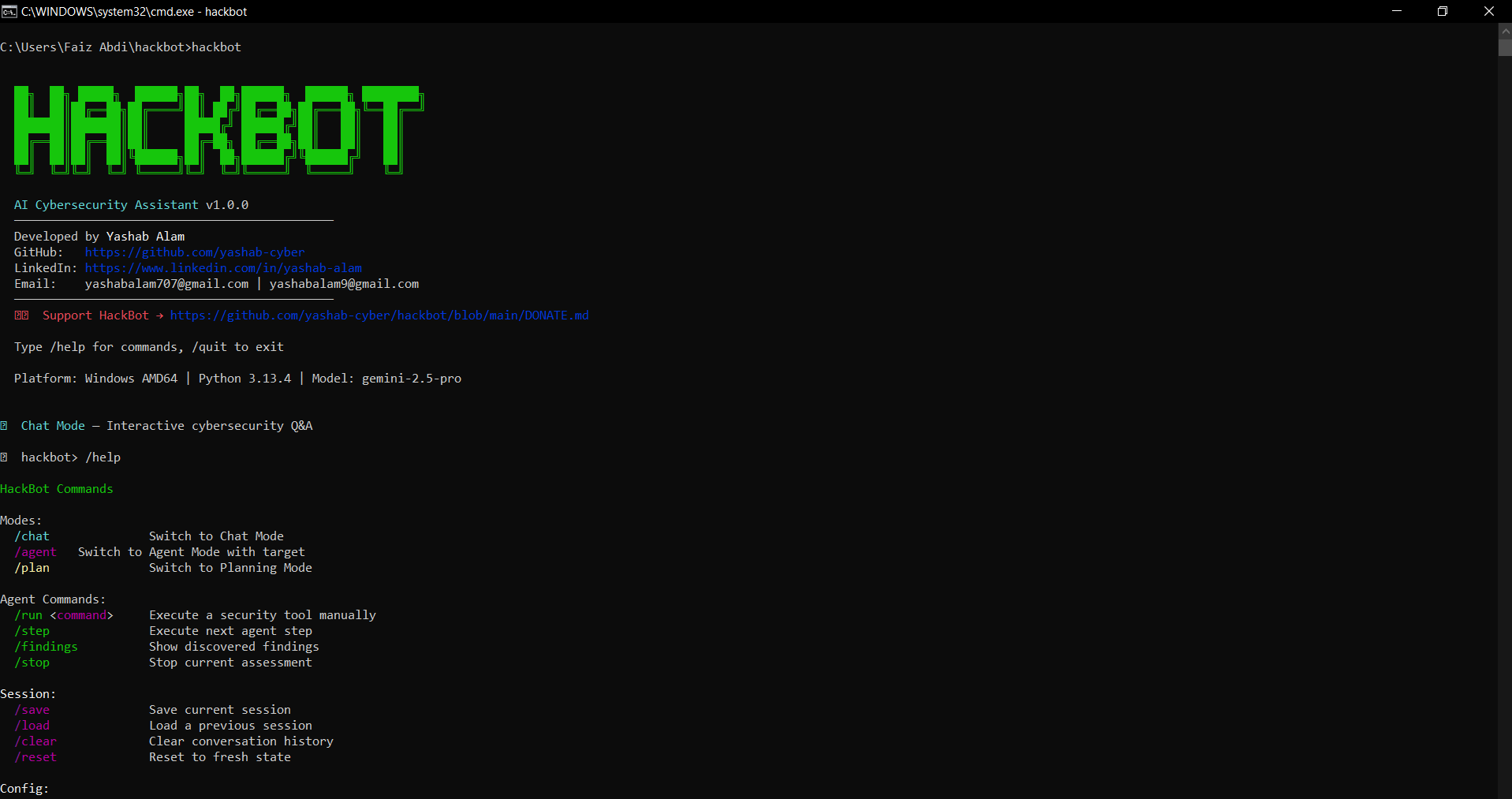 |
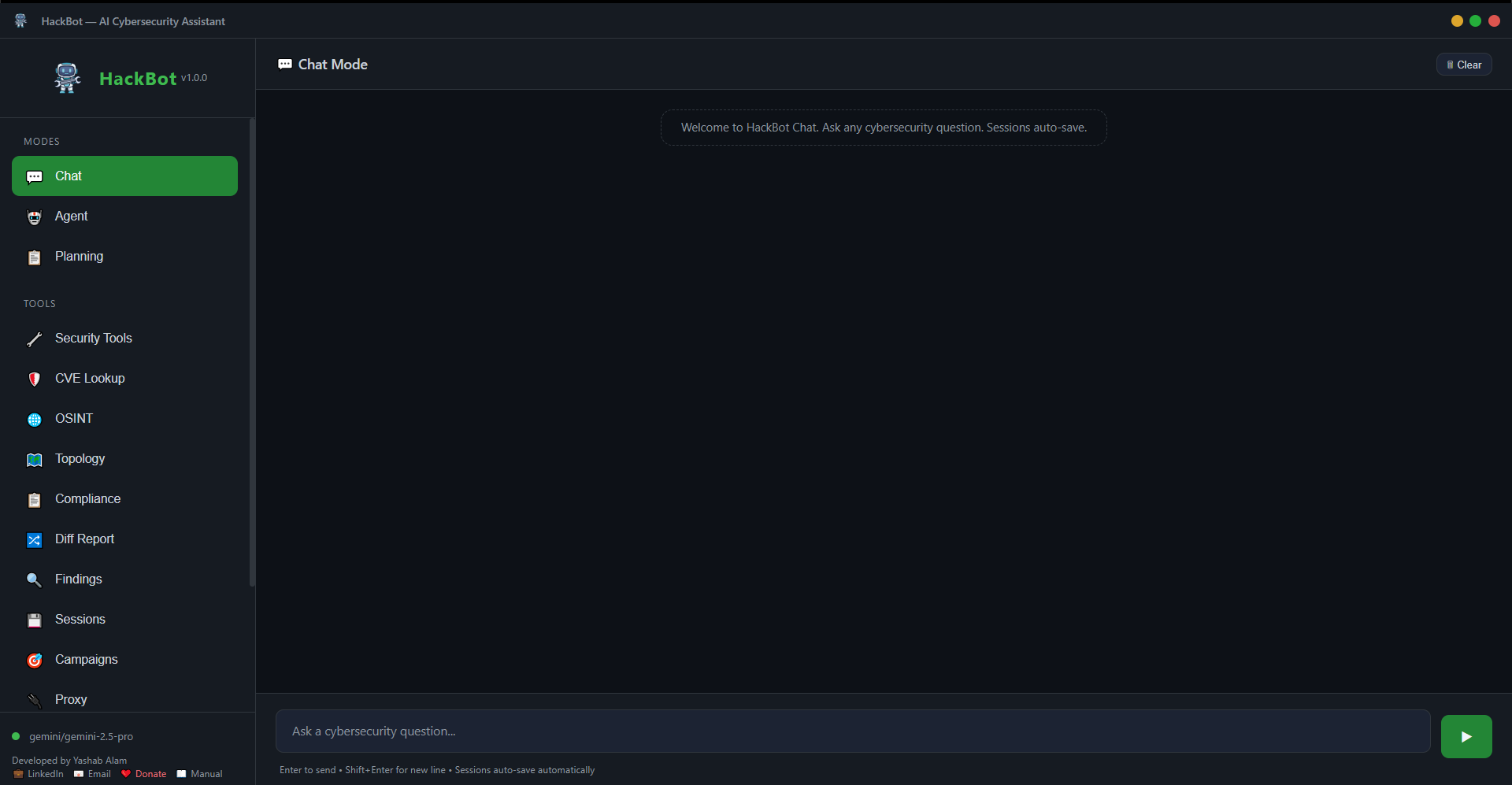 |
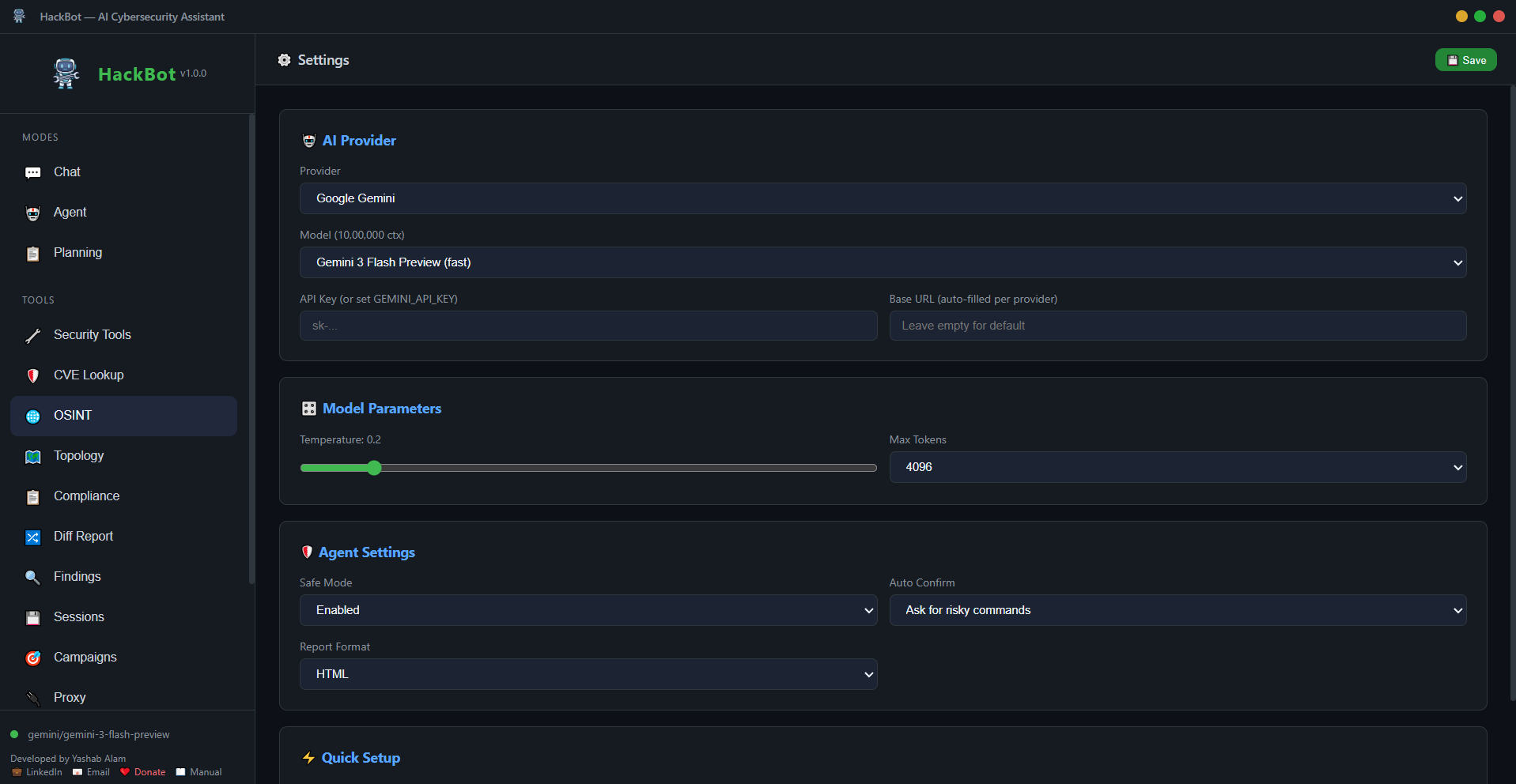 |
📦 Installation
# One-line install
pip install "hackbot @ git+https://github.com/yashab-cyber/hackbot.git"
# With all extras
pip install "hackbot[all] @ git+https://github.com/yashab-cyber/hackbot.git"
# Docker
docker compose up -d🤖 Local Models (No API Key Needed)
ollama pull xploiter/pentester
hackbot --provider ollama --model xploiter/pentester📖 Documentation
Full manual available in the manual/ directory.
Author: Yashab Alam • Support HackBot